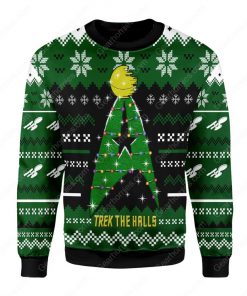
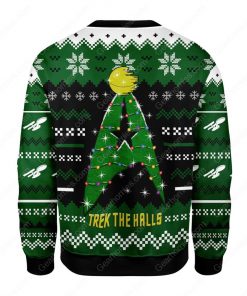
1. Choose style, color and size.
The above atributes are always available and suitable for the design, please do not hesitate to choose your favorite product.
Please see our
2. Click Add to cart.
Tip: Buying 2 or more products significantly reduces delivery costs.
3. Go to the checkout page.
Fill out the order information and proceed with payment.
4. The system will send a confirmation email when the order is complete.
Note:
If you receive a defective product due to printing or shipping, please contact us to get a new replacement product for free.
If you have any questions, please chat with us or contact us via [email protected]. Your satisfaction is our happiness. Thank you for trusting and shopping with us!